Sources: Amazon Web Services Security Blog (CJ Moses, CISO, Amazon Integrated Security), The Hacker News, The Register, Bleeping Computer, Cybersecurity News. Story broke March 18, 2026. Active threat, unpatched systems remain at risk.
Table of Contents
- The Attackers Had 36 Days That Nobody Knew About
- Who Interlock Is and Why They Are Particularly Dangerous
- CVE-2026-20131: What a CVSS 10.0 Vulnerability in a Firewall Actually Means
- How Amazon Found the Attack: The MadPot Honeypot Story
- The Misconfigured Server That Exposed Their Entire Playbook
- The Full Attack Chain: From Firewall Exploit to Ransomware Deployment
- ClickFix: The Social Engineering Trick That Bypasses Everything
- Slopoly: The AI-Written Malware Nobody Recognized
- The Third Threat: They Are Now Threatening to Report You to Regulators
- Are You Affected? How to Check Right Now
- The Bigger Problem This Exposes

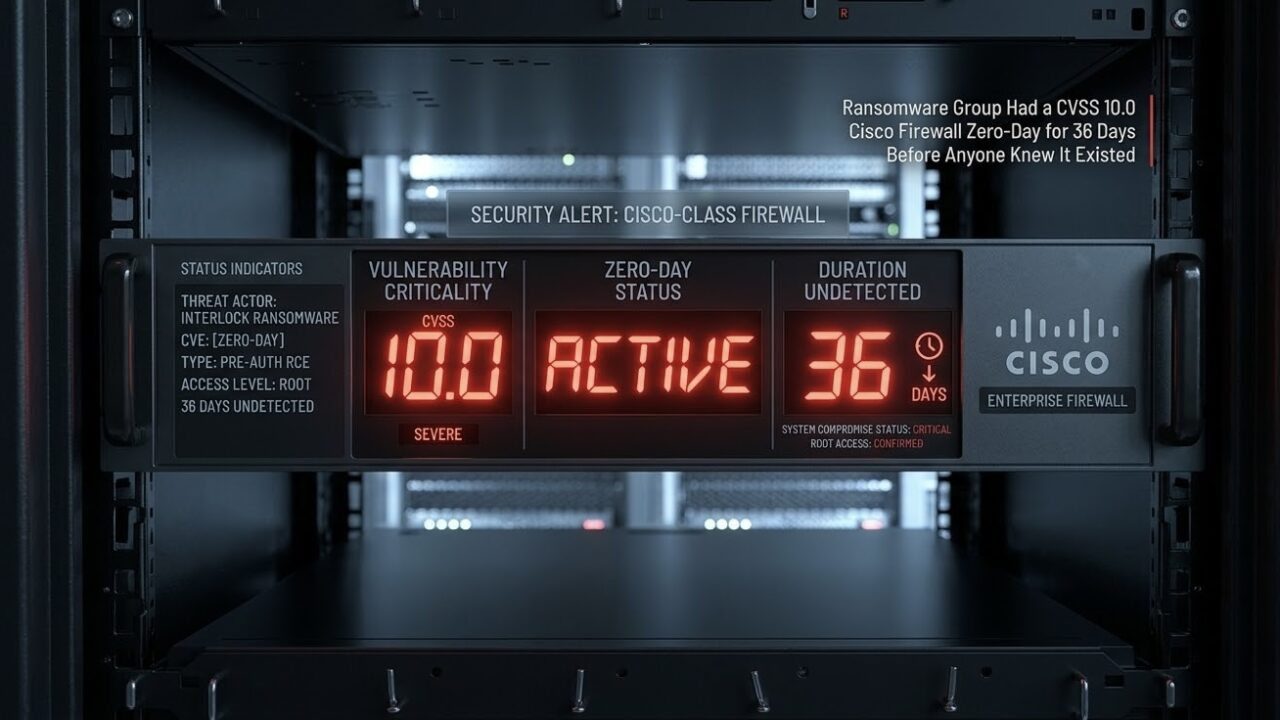
The Attackers Had 36 Days That Nobody Knew About
On March 4, 2026, Cisco published a security advisory for CVE-2026-20131, a critical vulnerability in Cisco Secure Firewall Management Center software. CVSS score 10.0, the maximum possible. An unauthenticated attacker anywhere on the internet could exploit it to execute arbitrary Java code as root on the affected device. If you run Cisco FMC, the management plane for your Secure Firewall deployment, Cisco was telling you to patch immediately.
What Cisco did not know on March 4, and what Amazon published on March 18, is that the Interlock ransomware group had already been exploiting that exact vulnerability since January 26. Thirty-six days before the public disclosure. Thirty-six days during which every organization running Cisco FMC was being actively hunted by a ransomware operation, with no patch available, no advisory published, and no way to know they needed to be looking for this specific attack.
That 36-day window is what makes this story different from a typical vulnerability disclosure. Zero-days that are found and patched before exploitation are common. Zero-days that get discovered only after being used for more than a month against real targets are rarer and more serious. Every organization that was compromised during those 36 days was compromised through a vulnerability that did not publicly exist. Standard patch management processes, which most security teams rely on as their primary defense against this class of attack, provided zero protection. The defenders were playing a game whose rules they did not know.
Active threat alert: Cisco released the patch for CVE-2026-20131 on March 4, 2026. If your organization runs Cisco Secure Firewall Management Center and has not applied this patch, you are exposed to active exploitation by a ransomware group with an established track record of hitting hospitals, disrupting chemotherapy, and leaking patient records. Check your FMC version immediately. Cisco’s advisory is at tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-fmc-rce-AHOZDPPe.
Who Interlock Is and Why They Are Particularly Dangerous
Interlock emerged as a ransomware operation in September 2024, which makes them a relatively young group by the standards of the ransomware ecosystem. What they lack in tenure they have made up for in targeting choices and operational sophistication. Their target history reads like a deliberate effort to maximize public visibility and pressure on victims: hospitals, healthcare networks, universities, and municipal governments.
DaVita, the kidney dialysis company that operates more than 3,000 facilities in the United States, was an Interlock victim. Kettering Health, an Ohio healthcare network, was hit in a way that disrupted chemotherapy sessions and pre-surgery appointments. Interlock then leaked cancer patients’ details online when the extortion negotiations did not go the way they wanted. The Texas Tech University Health Sciences Center was compromised. The city of Saint Paul, Minnesota, had 43 GB of files stolen, a breach significant enough that the Minnesota governor declared a state of emergency.
Hitting hospitals is a deliberate strategy rather than a random targeting choice. Healthcare organizations are under enormous pressure to restore operations quickly because system outages can directly affect patient care. That pressure increases willingness to pay ransoms. It also increases the reputational and regulatory risk of a disclosed breach, which gives the attackers additional leverage. A hospital that has just had chemotherapy disrupted and patient data stolen faces potential HIPAA penalties, class action lawsuits, and severe reputational damage simultaneously. Interlock has demonstrated they understand this leverage and will use it.
IBM X-Force researchers published findings in early 2026 that Interlock had deployed a new malware strain they named Slopoly, along with a remote access trojan called NodeSnake that was used in attacks against multiple UK universities. The same group has been linked to ClickFix campaigns, a social engineering technique discussed in detail below. Multiple attack vectors, custom tooling, a history of following through on data leak threats, and now a CVSS 10.0 zero-day in one of the most widely deployed enterprise firewall management platforms in the world. Interlock is not a script-kiddie operation running commodity tools.
CVE-2026-20131: What a CVSS 10.0 Vulnerability in a Firewall Actually Means
CVSS 10.0 is the maximum score on the Common Vulnerability Scoring System. It is not common. A score of 10 requires a vulnerability to be remotely exploitable without authentication, to have no user interaction requirement, to have no configuration dependency that limits the attack surface, and to provide complete compromise of the affected system. CVE-2026-20131 hits all of these criteria.
The technical classification is insecure deserialization of user-supplied Java byte stream in Cisco Secure Firewall Management Center. To understand why this is critical, deserialization is the process of converting data that has been serialized, compressed into a storable format, back into a live object in memory. When an application deserializes data that it received from an external source without first validating that the data is legitimate, an attacker can craft malicious serialized data that, when deserialized, executes arbitrary code. The “Java byte stream” part means the malicious payload is delivered as a specially crafted Java object. The “unauthenticated remote attacker” part means this happens before any login prompt. The attacker sends the crafted payload during the initial connection handshake and code execution happens before the application ever asks who they are.
The target here is not a random application. Cisco Secure Firewall Management Center is the management interface for Cisco’s enterprise firewall platform. Organizations use it to configure, monitor, and manage all their Cisco firewalls from a single pane of glass. Compromising FMC means compromising the management plane of the organization’s entire Cisco firewall infrastructure. An attacker with root access to FMC can read all firewall configurations, create new rules, disable existing rules, see all traffic the firewalls are monitoring, and potentially create backdoors through the firewall itself. A vulnerability in a firewall management system is, in a specific and meaningful way, a vulnerability in the firewall.
The scope of deployment is also relevant context. Cisco holds approximately 53 to 55 percent of the enterprise firewall market according to most recent market share estimates. Cisco Secure Firewall is one of the most widely deployed enterprise security products on earth. A CVSS 10.0 vulnerability in its management center, exploited as a zero-day for 36 days, has a potential victim pool that is very large.
How Amazon Found the Attack: The MadPot Honeypot Story
Amazon did not discover Interlock’s exploitation of CVE-2026-20131 by monitoring their customers. AWS infrastructure and customer workloads were not involved in this campaign. They found it through MadPot, Amazon’s global honeypot network, which is one of the more interesting threat intelligence systems in the industry.
A honeypot is a deliberately vulnerable system deployed specifically to attract attackers. When an attacker interacts with it, security researchers can observe everything they do: the tools they use, the commands they run, the infrastructure they connect to, and the payloads they deliver. MadPot is Amazon’s global-scale version of this concept, a distributed network of honeypot servers positioned to attract and monitor cybercriminal activity across the internet. When Interlock’s exploit traffic hit MadPot sensors, Amazon’s threat intelligence team could observe the full attack in a controlled environment.
The way Amazon advanced their investigation is particularly notable. After observing the initial exploit traffic, the Amazon team made a deliberate decision to act as a successfully compromised system. They performed the expected HTTP PUT request that the Interlock infrastructure was waiting for, with the expected file content, essentially telling the attacker’s automated system “yes, this target was successfully exploited.” This successfully prompted Interlock to proceed to the next stage of the attack chain and issue commands to fetch and execute a malicious ELF binary from a remote server. By pretending to be a compromised victim, Amazon’s researchers were able to observe the complete post-exploitation sequence that real victims were experiencing, without any real organization being harmed in the process.
This kind of active engagement with attacker infrastructure is threat intelligence tradecraft that most organizations cannot do. Amazon could, did, and then published the results publicly, including the complete attack chain, indicators of compromise, and infrastructure details that defenders can use. CJ Moses, Amazon’s chief information security officer, shared findings directly with Cisco to support their investigation before any public disclosure.
The Misconfigured Server That Exposed Their Entire Playbook
During the investigation, Amazon’s threat intelligence team identified something operationally significant: a misconfigured Interlock infrastructure server that had inadvertently exposed the group’s complete attack toolkit to the internet. The server was meant to be internal infrastructure. A configuration error made its contents publicly accessible.
This kind of operational security mistake is not rare in cybercriminal operations. Groups that are sophisticated in their attack techniques are not always equally sophisticated in their infrastructure management. The practical consequence for defenders is that Amazon was able to obtain and publish details about Interlock’s complete operational toolkit, not just the CVE-2026-20131 exploit chain but the full set of tools the group uses across its operations.
The exposed toolkit includes several notable components. A PowerShell script designed for initial reconnaissance collects detailed information about compromised Windows environments: operating system and hardware details, running services, installed software, storage configuration, and other system inventory data. This reconnaissance output is what tells the attackers how valuable the target is and how to proceed with the attack. A JavaScript browser implant is another toolkit component that specifically overrides browser console methods to hide from malware detection tools, then uses PowerShell and Windows Management Instrumentation to collect additional host information including system identity, domain membership, username, OS version, and privilege context. This data is encrypted and sent to the attacker’s command-and-control server via persistent WebSocket connections.
The fact that Interlock’s toolkit is now publicly documented by Amazon is genuinely useful for defenders. Endpoint detection and response tools can be updated with signatures for these specific components. Security teams can hunt for the specific behaviors, the PowerShell reconnaissance patterns, the WMI queries, the WebSocket C2 connections, in their existing telemetry to identify potential compromises that predate the patch. The exposure of the toolkit partially compensates for the 36-day head start Interlock had during the zero-day window.
The Full Attack Chain: From Firewall Exploit to Ransomware Deployment
The complete attack sequence that Amazon documented, from initial exploitation of CVE-2026-20131 through to ransomware deployment, follows a structured pattern that is consistent across Interlock’s known operations. Understanding the full chain is useful because each stage represents an opportunity to detect and interrupt the attack before it reaches the destructive endpoint.
The initial exploitation uses specially crafted HTTP requests to the affected path in Cisco FMC software. The request body contains Java code execution attempts and two embedded URLs: one delivers configuration data supporting the exploit, and one is designed to confirm successful exploitation by causing the vulnerable target to perform an HTTP PUT request uploading a generated file. This confirmation mechanism is what Amazon’s team exploited to gain visibility into the post-exploitation sequence. Once the confirmation fires, Interlock’s infrastructure proceeds automatically, issuing commands to fetch and execute a malicious ELF binary, a Linux executable, from a remote server.
From the initial foothold on the FMC device, the attack moves into the broader network. The PowerShell reconnaissance script runs to inventory the environment and identify high-value targets. The JavaScript browser implant is deployed on relevant endpoints. NodeSnake, Interlock’s custom remote access trojan, establishes persistent access channels that survive reboots and are harder to detect than standard remote access tools. These persistence mechanisms are what make Interlock attacks particularly difficult to remediate: a victim that removes the ransomware payload but misses a NodeSnake implant will find the attackers return.
Data exfiltration occurs before encryption in Interlock operations, which is standard for double-extortion ransomware. The stolen data becomes the leverage for the second ransom demand even if the victim successfully recovers from backups. The encryption itself is the final and most visible stage, designed to be undeniable and to create immediate operational pressure. At Kettering Health, that pressure manifested as disrupted chemotherapy sessions and cancelled pre-surgery appointments. At Saint Paul, it forced the city to declare a state of emergency. Interlock uses high-visibility targets specifically because the operational disruption amplifies the pressure to pay.
ClickFix: The Social Engineering Trick That Bypasses Everything
Alongside the Cisco FMC exploit campaign, Interlock continues to use a social engineering technique called ClickFix for initial access against targets where they do not already have an exploitable vulnerability. ClickFix is worth understanding separately because it is increasingly common across multiple threat actor groups and because it bypasses essentially every traditional endpoint security control.
The attack works as follows. The target receives a message, through email, a website popup, or a fake error dialog, claiming that there is a problem that needs to be fixed. A software error. A verification requirement. A missing plugin. The message provides specific instructions for how to fix it, which always involve opening a command prompt or PowerShell window, pasting a command, and pressing Enter. The command is the malicious payload. The entire mechanism works because the user is performing the action themselves, which means it bypasses application control policies, script execution restrictions, and many endpoint security tools that look for processes launching other processes. The user launched the malicious command directly, making it indistinguishable from legitimate administrative activity at the process level.
ReliaQuest’s technical analysis of Interlock’s ClickFix campaigns noted that the second important technical element is a staged command-and-control loader built on the Deno JavaScript runtime that executes malicious payloads directly in memory, without writing files to disk. Fileless execution is specifically designed to evade endpoint security tools that look for malicious files being written or executed from the file system. A payload that never touches the disk is harder to detect and leaves fewer forensic artifacts. The combination of social engineering that bypasses application controls and a fileless execution approach that bypasses file-based detection is what makes ClickFix campaigns effective against organizations with mature security postures.
Slopoly: The AI-Written Malware Nobody Recognized
IBM X-Force researchers identified a new malware strain in Interlock’s toolkit that they named Slopoly. The notable characteristic is that X-Force believes Slopoly was developed using generative AI tools. This is not a speculation: the code exhibits specific patterns, including unusual comment density, structured error handling that is more methodical than human programmers typically write, and variable naming conventions that are consistent with AI-generated code rather than the idiosyncratic styles that individual human developers develop over time.
AI-assisted malware development represents a meaningful change in the threat landscape for several reasons. Writing functional malware has historically required significant programming skill, which served as an implicit barrier limiting who could develop new malware tools. Generative AI substantially lowers that barrier. More practically, AI-generated code tends to be structurally different from human-written code in ways that can defeat signature-based detection. Most malware signatures are trained on large datasets of human-written malicious code. AI-generated code that achieves the same malicious outcomes through different structural patterns may not match those signatures.
Slopoly is specifically a backdoor, a persistent remote access mechanism that allows Interlock operators to maintain access to compromised systems after initial deployment. Its detection by IBM X-Force is a reminder that threat intelligence firms actively reverse-engineer captured malware and publish findings that feed into the security community’s collective detection capability. But the detection lag between new malware being deployed and detection signatures being widely distributed means there is always a window during which new variants circulate undetected. For AI-generated malware that is easy to iterate and regenerate in new structural variants, that window is a persistent advantage for attackers.
The Third Threat: They Are Now Threatening to Report You to Regulators
Ransomware extortion has traditionally operated with two main levers. The first is encryption: pay us or you cannot access your own systems and data. The second is data leak: pay us or we publish the data we stole. Interlock is now using a third lever that is newer and specifically calibrated to amplify pressure on regulated industries.
Amazon’s analysis of the ransom note used in this campaign found that in addition to the standard encryption and data leak threats, Interlock specifically threatens to expose victims to regulators, using the pressure of fines and compliance violations as an additional incentive to pay. The practical implication: if you are a HIPAA-covered healthcare organization and Interlock has your patient data, they are explicitly threatening to report your breach to the Department of Health and Human Services before you do. If you are a financial institution under SOX or GLBA, they are threatening to notify your regulators before you have a chance to manage the disclosure on your own terms.
The threat is credible because self-reporting a breach to regulators, while legally required, gives the organization some control over the timing and framing of the disclosure. An attacker that reports the breach to regulators first, with evidence of the stolen data, removes that control entirely. HIPAA penalties for healthcare breaches can reach $1.9 million per violation category per year. The combination of the fine exposure and the loss of control over disclosure timing creates meaningful financial and reputational pressure beyond the immediate operational disruption of the encryption itself. Interlock has specifically observed that healthcare targets are particularly sensitive to this third lever, which explains their persistent targeting of hospitals and health systems.
Are You Affected? How to Check Right Now
The immediate question for any organization running Cisco security products is whether they are exposed to CVE-2026-20131 specifically. Cisco released a patch on March 4, 2026. If your Cisco Secure Firewall Management Center has been updated since March 4, you are protected from the specific vulnerability Interlock has been exploiting. If it has not, you need to treat this as an emergency patch situation given that active exploitation has been ongoing for nearly two months.
Checking your FMC version is straightforward from the management interface. Navigate to Help, then About, in the FMC web interface. The version number will be displayed. Cisco’s advisory at tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-fmc-rce-AHOZDPPe lists the affected versions and the fixed releases. If your version is in the affected range and you have not applied the fix, that is the first action item, before anything else described in this article.
Beyond the patch check, organizations that ran vulnerable FMC versions between January 26 and March 4 should treat themselves as potentially compromised regardless of whether they have observed symptoms. The Interlock toolkit includes persistent access mechanisms that are designed to survive reboots and evade detection. The absence of obvious ransomware deployment does not mean the network was not accessed. The attack chain described by Amazon suggests a staged approach where initial exploitation, reconnaissance, and persistence establishment could all occur before any visible disruption, with the disruptive ransomware deployment potentially coming weeks later when Interlock has fully mapped the environment and staged the data exfiltration.
The specific indicators of compromise Amazon published for hunting in existing telemetry include the PowerShell reconnaissance script behaviors, specifically WMI queries for hardware and software inventory followed by exfiltration of that inventory data, and the WebSocket-based command-and-control communications associated with the JavaScript browser implant. If your security information and event management platform has logs covering the January 26 to March 4 window, hunting for these patterns against systems that were communicating with your FMC infrastructure is the highest-priority investigation action for affected organizations.
The Bigger Problem This Exposes
CVE-2026-20131 and Interlock’s 36-day head start illustrate a structural problem in enterprise cybersecurity that the Cisco vulnerability makes visible but did not create. The entire patch management model, which is the primary defense mechanism for most organizations against this class of attack, is fundamentally reactive. It protects against known vulnerabilities. It provides no protection against unknown ones. And the attackers know this.
The 36-day exploitation window is not unusual. Google Project Zero’s research on zero-day vulnerabilities in 2024 found that the median time from first exploitation to patch release for zero-days actively used in attacks was 24 to 70 days depending on the vendor and vulnerability class. Some zero-days are exploited for significantly longer, including several that ran for more than a year before being discovered and patched. The Interlock case is notable because Amazon’s threat intelligence capability was sophisticated enough to find it relatively quickly and because the target is a security product rather than a general-purpose application. But the pattern of exploitation well before disclosure is not exceptional.
What this means practically is that patch management, while necessary, is not sufficient as the primary defensive strategy for high-risk systems. The additional controls that matter most for the class of threat Interlock represents are the ones that assume the perimeter has already been penetrated: network segmentation that limits what an attacker who has compromised a management system can reach, behavioral detection that identifies reconnaissance activity and unusual lateral movement patterns regardless of what vulnerability enabled the initial access, and privileged access management that restricts what can be done from management interfaces even by authenticated sessions.
Interlock’s use of a CVSS 10.0 zero-day in a firewall management system to hit hospitals and municipal governments is an escalation that is difficult to overstate. Firewalls are supposed to be a defensive layer. Compromising the management plane of an organization’s entire firewall infrastructure from the internet, before authentication, with no prior knowledge required, turns the defensive layer into an attack surface. Cisco’s response to this specific vulnerability, once notified, was appropriate: they patched quickly and updated their advisory when Amazon provided the exploitation evidence. The question for organizations running enterprise security infrastructure is whether their operational monitoring would detect this kind of attack if it happened to them before Amazon noticed it in a honeypot.
For most organizations, the honest answer is probably not quickly enough. That gap between what attackers can do and what defenders can detect is what makes stories like this one important to understand rather than just to read about.
Are you running Cisco Secure Firewall Management Center? Drop your current version in the comments and I will confirm whether it is in the affected range. Also interested to hear from anyone in healthcare IT on how the regulatory extortion threat is changing their ransomware response planning. That third lever is new enough that most incident response playbooks have not been updated to account for it.
References (March 19, 2026):
Amazon Web Services Security Blog, CJ Moses (Amazon CISO): “Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewalls” (March 18, 2026): aws.amazon.com
The Hacker News: “Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access” (March 18, 2026): thehackernews.com
The Register: “Ransomware crims abused Cisco 0-day weeks before disclosure” (March 18, 2026): theregister.com
Bleeping Computer: “Ransomware gang exploits Cisco flaw in zero-day attacks since January” (March 18, 2026): bleepingcomputer.com
Cybersecurity News: “Cisco Firewall 0-day Vulnerability Exploited in the Wild to Deploy Interlock Ransomware” (March 18, 2026): cybersecuritynews.com
IBM X-Force: Slopoly AI-generated malware discovery (2026): IBM Security Intelligence
ReliaQuest: Interlock ClickFix and Deno-based C2 loader technical analysis (March 2026)
Cisco Security Advisory CVE-2026-20131 (patched March 4, 2026): tools.cisco.com
The firewall was supposed to be the thing protecting you from attackers.
For 36 days, it was the thing they were walking through.



Leave a Reply